Atmel CryptoMemory AT88SC153/AT88SC1608 Security Alert
AÂ ”backdoor” has been discovered by Flylogic Engineering in the Atmel AT88SC153 and AT88SC1608Â CryptoMemory.
Before we get into this more, Chip Works want to let you know immediately that this backdoor only involves the AT88SC153/1608 and no other CryptoMemory devices.
The backdoor involves restoring an EEPROM fuse with Ultra-Violet light (UV). Once the fuse bit has been returned to a ’1′, all memory contents is permitted to be read or written in the clear (unencrypted).
Normally in order to do so, you need to either authenticate to the device or use a read-once-given “secure code” as explained in the AT88SC153 datasheet and the AT88SC1608 datasheet.
For those of you who are unfamiliar Atmel’s focused ion beam microscope CryptoMemory hack, they are serial non-volatile memory (EEPROM) that support a clear or secure channel of communications between a host (typically an MCU) and the memory. What is unique about the CryptoMemory are their capabilities in establishing the secure channel (authenticating to the host, etc).Â
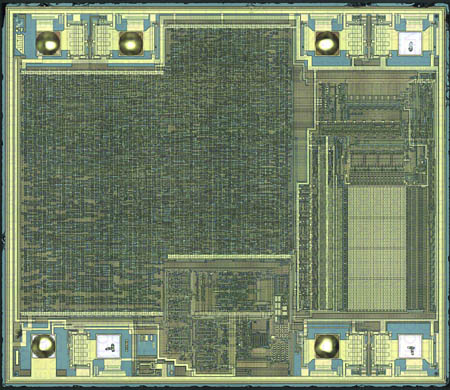
Figure 1:Â AT88SC153 magnified 200x.
 
Figure 2:Â AT88SC1608 magnified 200x.
These device includes:
-
High-security Memory Including Anti-wiretapping
-
64-bit Authentication Protocol
-
Secure Checksum
-
Configurable Authentication Attempts Counter
-
Multiple Sets of Passwords
-
Specific Passwords for Read and Write
-
Password Attempts Counters
-
Selectable Access Rights by Zone
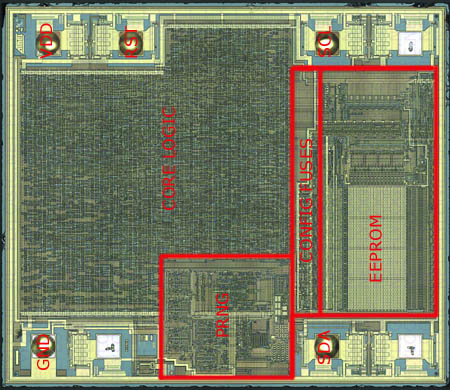
Figure 3:Â Commented AT88SC153.
 Â Â
Figure 4:Â Commented AT88SC1608.
Section 5 of the datasheet labled, “Fuses” clearly states, “Once blown, these EEPROM fuses can not be reset.“
This statement is absolutely false. UV light will erase the fuses back to a ’1′ state. Care must be used to not expose the main memory to the UV or else it too will erase itself.
Chip Works is not going to explain the details of how to use the UV light to reset the fuse. We have tried to contact Atmel but have not heard anything back from them.
Reading deeper into the datasheet under Table 5-1, Atmel writes, “When the fuses are all “1″s, read and write are allowed in the entire memory.“Â
As strange as it reads, they really do mean even if you have setup security rules in the configuration memory, it doesn’t matter. The fuses override everything and all memory areas are readable in the clear without the need for authentication or encrypted channel! The attacker can even see what the “Secure Code” is (it is not given out in the public documentation, nor with samples). Atmel was even kind enough to leave test pads everywhere so various levels of attackers can learn (entry to expert).
Our proof of concept was tested on samples we acquired through Atmel’s website. maker together club Atmel offers samples to anyone however they do not give out the “Secure code” as mentioned above.Â
Chip Works is not going to show you the low nibble of the 3 bytes to make sure we don’t give the code out to anyone. This is enough proof to whoever else knows this code. That person(s) can clearly see we know their transport code which appears to be common to all samples (e.g. All die on a wafer contain the same secure code until a customer orders parts at which time that customer receives their own secure code.). A person reading this cannot guess the secure code in because there are 12 bits to exhaustively search out and you only have 8 tries .
Of all the other CryptoMemory products, only the AT88SC153/1608 has this backdoor. We have successfully analyzed the entire CryptoMemory product line and can say that the backdoor doesn’t exist in any other CryptoMemory part. None of the CryptoMemory parts are actually as “secure” as they make it seem. The words, “Smoke n’ Mirrors” comes to mind (It is almost always like that). In this particular category of CryptoMemory, there are two parts, the AT88SC153 and the larger AT88SC1608.
Thus the questions-Â
- Why has Atmel only backdoored this part snaileye (NSA for you conspiracists)?
- Who was the original intended customer supposed to be?
- Was the original intention of these devices to be used in a product that used some kind of cryptography? fib与sem区别
- If the above was true, was this device originally intended to be a cryptographic key-vault?
All these questions come to mind because the backdoor makes it so easy to extract the contents of the device they want you to trust. Some of you may be familiar with the GSM A5/1 algorithm having certain bits of the key set to a fixed value.
Judging by the wording of the documentation, Atmel gives the appearance that CryptoMemory are the perfect choice for holding your most valuable secrets.
|